Risk Management
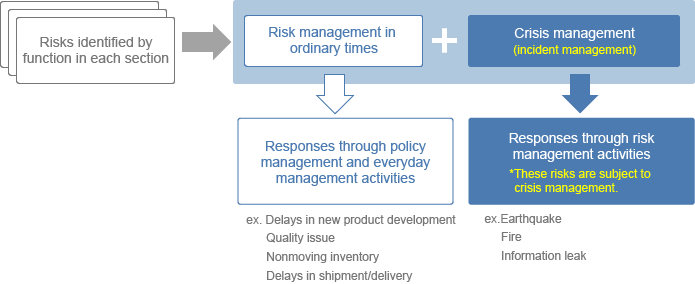
COSEL has established Risk Management Regulations and addresses corporate risks in accordance with the following flow chart.
In normal times, each department plays the main role in risk management, which is treated as an item subject to annual policy management and daily management in each department as part of its policy management activities.
For crisis management in response to such contingencies as disasters, accidents, and fires, we have established Regulations on Responding to Crisis Situations under which we give top priority to protecting human life, rescue, and minimizing the impact on customers in accordance with the Emergency Initial Response Manual. In addition, the Risk Management/Compliance Committee reviews and assesses subject risks and studies and implements related countermeasures.
In addition, we have established the Business Continuity Plan (BCP) Regulations and maintain a system to enable the swift resumption of business operations in response to contingencies.
< Outline of risks >
Information Security
As a company manufacturing and selling switching power supplies and EMI filters, we consider it our social responsibility to protect the information assets that we possess, including those of our clients. We hereby establish the basic policy for information security and declare that we will follow it.
- 1.We will establish a system to promote information security to manage the information assets properly.
- 2.We will provide education necessary to ensure information security.
- 3.We will introduce proper management measures and work hard to prevent information security incidents and accidents from occurring.
- 4.In cases where information security incidents or accidents occur, we will promptly investigate the cause and work hard to minimize damage and prevent a reoccurrence.
- 5.We will comply with laws and regulations, national guidelines, and other social norms relating to information security.
- 6.All employees shall comply with rules and regulations relating to information security, and we will implement punitive measures against those who violate them in accordance with our internal rules and regulations.
- 7.We will develop and implement internal rules and regulations in accordance with this basic policy.
- 8.We will maintain the activities mentioned above and strive to improve them continuously.